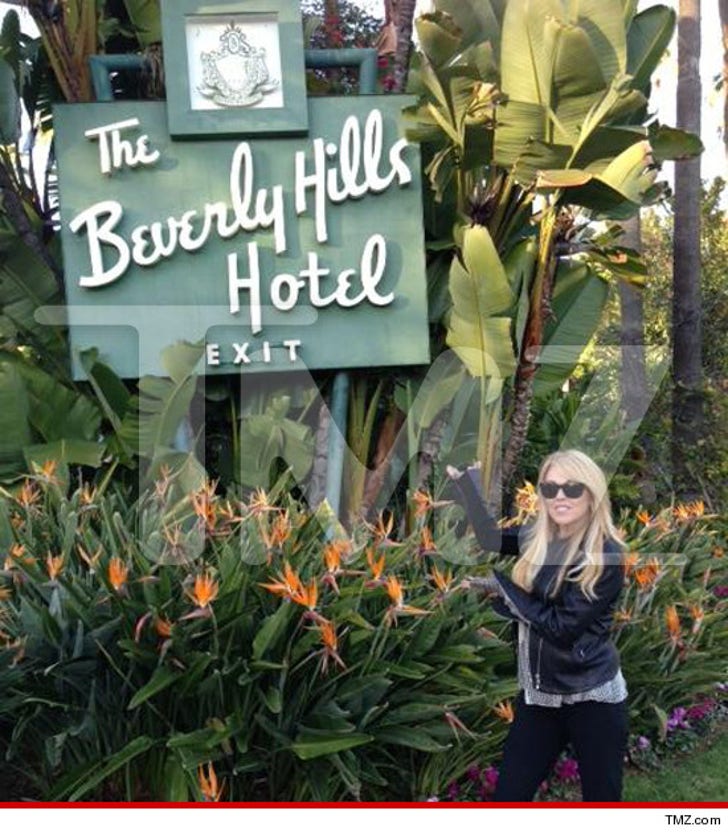
Dina Lohan -- We're Shacking Up in Beverly Hills
Dina Lohan We're Shacking Up in Beverly Hills
Lindsay Lohan's hotel rejection streak is OVER ... 'cause she and her mother Dina were finally able to score a room at the legendary Beverly Hills Hotel ... TMZ has learned.
We broke the story ... LiLo and DiLo were turned away from TWO famous hotels in Santa Monica late last night ... after they arrived in L.A. for Lindsay's court hearing.
But the search continued ... and the Lohan ladies were finally able to find a suite in the Hills of Beverly ... at the same hotel where Howard Hughes lived on and off for 30 years.
In fact, the BHH has hosted some of the most famous people in the world ... including John Wayne, The Beatles ... and even Liz Taylor.
It's also where Harvey Levin famously asked Paris Hilton how she felt about TMZ users comparing her to a "fart in a mitten" back in 2006. Enjoy ...